Access Control Softwares (673)

View and process alarms Monitor and override the status of doors and zones Lockdown zones quickly Trigger macros to perform custom functions Log mobile actions and events in Command Centre \ Disable a cardholder’s access QR and Barcode scanning for quick identification Receive notifications from Command Centre (Android devices must have the Google Play App installed)
Add to Compare
This application provides all the functionality to monitor or control the access of vehicles to a site. A typical system would comprise of a camera monitoring thea ccess road, a number plate recognition computer with Talon ANPR and access control software installed, and optional barriers and traffic lighting.The software can be configured to meet your requirements and contains the abilityto set up separate sub-databases e.g. White list (vehicles that have authorised entry) & Black list (vehicles that are refused entry). It will allow only authorised vehicles to enter, keep track of the number of spaces available and deny access to unrecognised vehicles. These features improve safety and security for both car park and vehicle owners. Frequent visitor lists can also be used for marketing and statistical data. The software can also be used to control hardware such as barriers and traffic lights through the simple addition of Input / Output cards to be fitted into the recognition computer.
Add to Compare
Store access credentials for multiple sites Use long range access with Bluetooth® wireless technology Store their fingerprint or PIN data on the mobile device, privately and securely using FIDO open standard authentication security Interact with building systems Receive important site notifications
Add to Compare
Access Groups is a powerful and efficient cardholder management tool which divides cardholders into groups depending on criteria and determines access privileges. Group information can include: Where and when the group has accessA list of members of the groupPersonal data fields for group membersWhether group members are allowed to act as escorts for visitorsAuthorization to arm and disarm alarm zonesWhether group members can change the state of access zones
Add to Compare
Administers system with a simple to use interface in a web-browser without having to install additional software View live and archived footage with a powerful built in video management system Create a system spanning multiple sites and/or subnets, for control and management from a single remote user interface Scalable up to 100 sites on a single system with up to 1,000 doors, 1,000 cameras and 50,000 users Log into the system from a web-browser anywhere in the world with an internet connection Administer system on mobile devices with the free Paxton Connect app that can be used off site Use smartphone or smartwatch in place of traditional tokens with the free Paxton Key app Customise view of Paxton10, create widgets and build dashboard, combining video, site plans, events and building controls Fully customisable software permissions allow to give tailored access to particular areas of the software, reports, dashboards or users Create effective landlord/tenant scenarios with customisable building permissions and folder structures, with access only for specific user Use the software to control devices on the system; for example, open a door Import images for a visual representation of site, to monitor access, control devices or view video simply and easily Easily create rules based on system events, including controlling other doors, devices or arm/disarm the intruder alarm Prevent a user from passing their token back to a second person to gain entry into the same controlled area Create reports listing all users currently within a specified area. In the event of an emergency this helps to confirm all users have evacuated safely
Add to Compare
OnGuard GO! supports up to 32 devices (64 readers), 5000 cardholders, 32,000 access levels, 8 card formats, 512 inputs, 512 outputs, up to 30 transactions per minute and a USB capture device. The system also supports peripheral devices with industry standard communication drivers, including credential printers (Nisca, Eltron, Magicard), network connectivity devices (Lantronix) and readers (magnetic stripe, Wiegand, proximity, bar code, smart card and biometric).
Add to Compare
CEM SWENET128 is an Ethernet reader controller software for 128 doors. It is a software controller required for use with Ethernet based CEM readers and devices as part of the AC2000 SE (Standard Edition) and AC2000 AE (Airport Edition) access control systems. The RTC is used with CEM Ethernet devices such as the emerald touch screen reader, S610e reader, S610f reader, Etherprox reader, S3030 portable reader range, eDCM 300 (Door Control Module), eDCM 300 Input/Output Module and the EIOC (Ethernet Input/Output Controller). The RTC Ethernet software offers an added layer of system resilience as it is capable of operating independently from the central CDC server should communications between the two be temporarily lost.
Add to Compare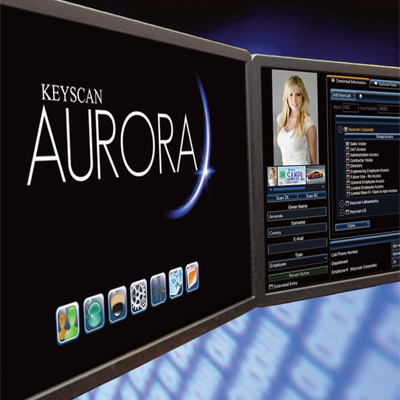
Keyscan AURORA is an access control management software. The software features support for 45,000 credentials, new multi-threaded communication structure, web interface and more. The new communication structure provides simultaneous communication to all IP nodes. It features robust integration support for many VMS, DVR and NVR systems including Keyscan DVR, Milestone, ONSSI, i3 International, Exacq, Open Eye CCTV and E-Series, Salient Systems, and Avigilon. It also features multi-language support, photobadging, visitor management, as well as system task scheduling.
Add to Compare
LiNC-NXG PIV is the next generation of Federal security solution systems, meeting the control and security objectives requirements of FIPS and HSPD-12 standards. LiNC-NXG PIV utilises identification issued by the Federal departments and agencies for federal employees and contractors for gaining physical access to Federally controlled facilities. LiNC-NXG PIV utilises PIV Cards with Cardholder Unique Identifiers (CHUID) and includes an element of the Federal Agency Smart Credential Number (FASC-N). LiNC-NXG PIV also provides “personal privacy and confidentiality” of the system and user data.LiNC-NXG PIV’s communication architecture is industry unique.
Add to Compare
Access PE provides self contained access control for small and medium-sized companies. Its installation is extremely simple and fast. There is no need to install and administer a database system. The system is easy to use and enables a person with minimal training to create badges and administer access rights in a very short time. Specific event logging and reporting allows you to trace who was when and where on your company’s grounds.
Add to Compare
Designed to provide powerful access control and integrated security management solutions for most business applications Suitable for small to medium organisations requiring an access control and security management system that can use existing corporate networks Includes alarm management software, graphical maps, reports, a free video and visitor management system and many other powerful features In addition, a badge designer tool is included providing users with the ability to design and print identity badges Also includes database partitioning, which provides a cost-effective solution for buildings occupied by more than one organisation System access is also available from a web browser using the optional SymmetryWEB™ software Controls up to 512 card readers and 9 client computers as well as unlimited card holder capacity (10GB Max size database)
Add to Compare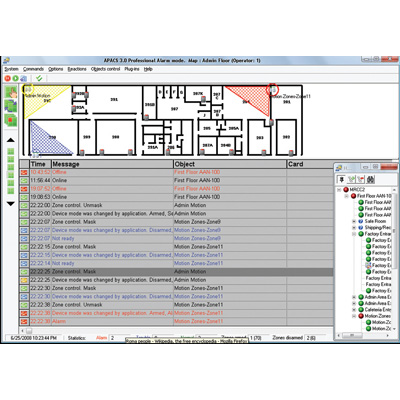
Apollo Security introduces its new APACS 3.4 access control and security integration software.Apollo Security's Access Control and Alarm Monitoring System (APACS) is the result of years of research and design coupled with real-world input from security professionals working at the most secure sites around the globe. APACS comprises the basis for a flexible and robust system that meets the needs of systems ranging from perimeter systems up to fully integrated enterprise-level installations.APACS 3.4 features include:Support for FIPS 201 compliant credentialsOPC Integration: Alarm & Event Support; OPC value writing via reactions, including OPC wrapper around data server to generate eventsSupport for Suprema BioMini enrollment readerSupport for L-1 Bioscrypt 4G readersReaction for Archive Video PlaybackStop unconditional reactionCopy feature for reactionsComments for message acknowledgmentsCustom Message Columns for event display in Alarm ModeCustom configuration file locationCommand line execution for ReportsButton to easily create temporary card and deactivate/activate permanent cardSupport for Samsung, Panasonic and Bosch video recordersImage support for Advanced FieldsSupport for SQL Server 2008Faster loading and closing of Guard Drag and drop icons onto APACS maps
Add to Compare
Access PE provides self contained access control for small and medium-sized companies. Its installation is extremely simple and fast. There is no need to install and administer a database system. The system is easy to use and enables a person with minimal training to create badges and administer access rights in a very short time. Specific event logging and reporting allows you to trace who was when and where on your company’s grounds.
Add to Compare
LiNC-NXG is a fully integrated physical security information management system (PSIM). PSIM is a category of systems designed to integrate multiple security applications controlling them through a comprehensive user interface (GUI). In a world of choices, LiNC-NXG offers multiple system configurations to fit your exact security needs. In addition to LiNC-NXG’s standard desktop solution, a browser managed interface is an available option. The browser based option eliminates software installation and maintenance requirements of application software. LiNC-NXG’s communication architecture is industry unique.
Add to Compare
LiNC-Ez / NRX Kit manages access control, alarm monitoring and building needs. All in one box! The ease begins right at installation with a self guided wizard to help load and configure system. With its enhanced preprogrammed access parameters and schedules, LiNC-Ez is ready to use immediately after installation. A complete two-door package that allows up to 12,000 cardholders and up to 64 doors.
Add to Compare
Keyscan K-BADGE photo badging & verification module integrates with System VII for a streamlined badging operation and offers the added benefit of greater security. It supports and prints a variety of industry-standard barcode types. It creates unlimited template designs to distinguish departments or areas of authorisation as well as shares cardholder images with other departments such as human resources. It displays cardholder image and transaction details immediately following site activity and has an “Always On Top” setting for constant monitoring of photo verification window even if other programs are open.
Add to Compare
Visitor Management is an optional licensed feature of Gallagher Command Centre, delivering extensive pre-registration and reception-based visitor management functions. Optional visitor self-registration capability is available using the touch-screen enabled Visitor Management Self-Registration Kiosk. The Kiosk allows visitors to sign-in for a visit independently of the receptionist. On completion of sign-in their host is automatically notified of their arrival via email or SMS. Hosts can manage their visitors onto and off-site from the Kiosk, including the ability to issue visitor cards and assign access, update the visit details or reprint visitor labels. Hosts of visitors who are overdue to leave are automatically notified for follow-up action.
Add to Compare
Identity Management On / Off Boarding Custom approvals workflow Policy creation Role based permissions Door Access provisioning Access Group management HR system integration Symmetry access control integration Automated Access Audits Compliance dashboards Compliance reports Badge Template Creation Photo ID Processing Self Service photo ID Self Service access provisioning
Add to Compare
LiNC-XS for Windows Server provides the power to customise complete access control systems to specific needs without requiring advanced technical expertise. This makes it ideal for a wide variety of applications such as multi-tenant office buildings, universities, hospitals, manufacturing facilities, government applications and more. It provides the same high degree of security and control from the most limited implementation to the largest, multi-site solution. LiNC-XS utilises a powerful set of security system integration solutions that provide total flexibility and control over a facilities security infrastructure, while reducing overall operating costs through seamless integration and system reliability. Seamlessly integrates access control, intrusion detection, video surveillance and recording, photo ID badging, smart cards, biometrics, elevator and parking control and the interoperability with other building and business systems.
Add to Compare
Import cardholder data, photos and access rights from third-party systems using flexible XML interfaces or the simple data mapping tool found within the Enterprise Data Import module. Assign access rights based on the type of day, time of day, area being accessed, validity of the cardholder token and any relevant competencies the cardholder possesses (such as training, licenses, inductions or medical clearances). Access changes are immediately and automatically downloaded to the controllers. Manage cardholder details, view recent cardholder events and track card replacement history. Perform bulk updates of cardholder information, such as a change in department. Design card layouts, and print and encode photo ID cards. Tailor screen layouts for the cardholder management team. Find cardholders in the system via access card presentation, text entry or multi-statement search criteria. Integrate intranet, web or network-based cardholder information directly to Command Centre via in-built browser capability. The integration of access control and intruder alarms allow a person with correct permissions to access a door as well as disarm an associated intruder alarm zone on entry, without requiring a separate keypad.
Add to Compare
Symmetry Mobile is a web credential application designed to be used with AMAG Technology’s Symmetry Bluetooth readers. Symmetry Mobile is a convenient solution for organizations using mobile devices or in conjunction with physical credentials for users who are transitioning to a mobile system to gain access to secured doors. It works with AMAG’s Symmetry Access Control system, as well as other access control systems, providing a seamless, efficient and cost-effective solution for enterprise users deploying more than one system. The touchless solution supports multi-factor authentication when used with a PIN or biometric (fingerprint or facial recognition) on both Android and Apple iOS devices. Users can type their PIN or use a biometric on their phone, eliminating the need to touch the reader and in support of COVID-19 guidelines. The frictionless setup of a credential eliminates the need to physically interact with the security team. Organizations can centrally issue and manage mobile credentials, photos and devices to their entire user base from a remote location, eliminating the need to buy and carry a physical credential and come into the badge office. The virtual credential in Symmetry Mobile displays a person’s name and photo. An unlimited number of credentials can be stored within their digital wallet, allowing people who need to access multiple sites using different access control systems to use the same mobile device. In an effort to support businesses that required employees to be on-site and ensure the health and safety of the labor force, AMAG developed a customizable health screening questionnaire to help reduce the risk of potentially infected employees from entering a building. Upon successful completion of the questionnaire, an employee’s physical access card or mobile credential will be enabled for a specified period of time, for example, one day. If the form is not completed successfully, the access card will expire and the employee will be denied access to the building. The system will send email notifications to managers for visibility. The questionnaire’s functionality operates independently and can be used on virtually any existing Symmetry Access Control system installation — and without any local infrastructure changes. Symmetry Mobile data is highly secure, as all of the data is encrypted when sent to the reader or stored on the phone, ensuring the mobile solution is completely secure. Users can customize the signal strength and read range on a per device and/or per person basis, increasing security and accommodating those who may need a longer read range, such as a person in a wheelchair, to open a door. Door read and unlock time is less than 1.2 seconds. Symmetry Mobile is available as a hosted or on-premise solution. The app is available in English, Spanish, French and Arabic, and is available now in the Apple App Store and Google Play Store.
Add to Compare
OnGuard Visitor is a dependable and cost effective visitor management application that enables an organization to manage and track visitors throughout its facilities, using standard desktop technology. Whether it is implemented as a standalone system or seamlessly integrated with other OnGuard application modules to create a total security management environment, OnGuard Visitor offers unlimited flexibility by allowing IT and security managers to further capitalize on existing IT investments in their facilities.
Add to Compare
Key features:Taking advantage of core software features within the industry-renowned AC2000 SE system and supporting CEM's range of industry leading hardware products, AC2000 Lite is setting the benchmark as one of the most accomplished security management solutions available for the small to mid-range markets. The AC2000 Lite has a system controller which any client workstation on the network can access to manage the database, monitor alarm activity or configure devices.Supporting up to 128 doors, AC2000 Lite comes fully-loaded with all the software required for performing all system tasks. This includes access control, ID badging, graphical alarms maps, vehicle management, visitor management, time & attendance and much more.Supports Power over Ethernet access control - CEM DIU 220 (Power over Ethernet Door Interface Unit) allows power and comms to be provided at the door via a single Cat 5/6 cable.Using the CEM DCM 300 intelligent two door IP controller, AC2000 Lite supports most third-party read heads conforming to the physical Wiegand interfaces, including support for third-party biometric technology. Supporting CEM's advanced range of IP card readers including the industry first S610e reader and with an on-board database, CEM's readers store transactions and operate offline, with the additional option of card plus PIN control. A graphical LCD display allows messages to be displayed such as ‘wrong zone', ‘lost/stolen card', ‘invalid card', ‘expiring card'.Easy system set-up - web-based configuration tool to perform the basic set-up and configuration of the AC2000 Lite Controller.
Add to Compare
Including interface advancements, enlarged vendor independency and compatibility with the latest Windows Internet Explorer 9, Bosch Security Systems introduces a number of updates to its Building Integration System (BIS). The new version 2.5, which is available from early May 2012, increases the range of supported devices to more than 1,000 different third party cameras and encoders, making it suitable for even the most complex integration projects. The new system allows further optimized security, safety and communication management in one front-end system with customized user interface. The range of video devices supported by BIS 2.5 is unmatched in the industry. It seamlessly interoperates with virtually any video camera, connecting to the latest IP cameras on the market with HD and H.264 encoding technology. The Divar 700 and Bosch Recording Station are supported in their most recent versions. BIS 2.5 benefits installers and end users alike: certified BIS partners and systems integrators enjoy an upgraded level of customization options, such as new layout formats for a wide range of monitor sizes (including 16:9 and 16:10). Thanks to numerous handy improvements, such as useful additions to the symbol libraries, it is now even easier to personalize the system. BIS 2.5 is interoperable with the large variety of ONVIF-compatible, modern IP-based video products supplied by all major manufacturers. ONVIF ensures a uniform standard, allowing customers to choose the product that best fits their individual needs, without having to worry about compatibility. It thereby saves costs and allows long term planning. The ONVIF standard was first introduced by a consortium of companies, including founding member Bosch, in 2008.
Add to Compare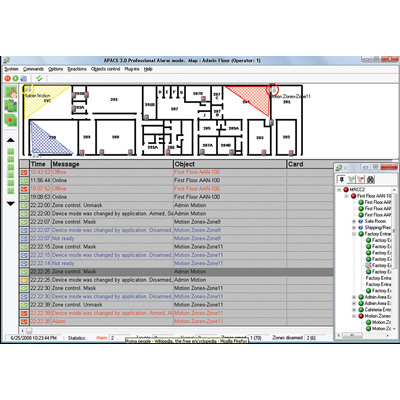
Apollo Security introduces its new APACS 3.3 access control and security integration software.Apollo Security's Access Control and Alarm Monitoring System (APACS) is the result of years of research and design coupled with real-world input from security professionals working at the most secure sites around the globe. APACS comprises the basis for a flexible and robust system that meets the needs of systems ranging from perimeter systems up to fully integrated enterprise-level installations.APACS 3.3 features include:Apollo Universal Video Interface (following video recorders supported):ApolloVision ApolloVideoPanasonic HD and ND BoschSalient SystemsHikvisionBiometric reader integration L1 and Suprema fingerprint and Schlage hand geometry readers Smart downloads to controllers, reader interfaces and biometric readersMore effective use of device memoryQuicker downloadsAccess Levels increased from 255 per system to 255 per controllerSupport for MS SQL Server 2008Support for Windows 7 operating systemActive Directory / Single sign-on See the image with captions
Add to Compare
Gallagher elevator integrations control access to floors with a high level interface (HLI) between an elevator system and Command Centre. An HLI achieves intelligent elevator control without relying on the excessive user interaction that a low level interface requires. Gallagher supports all leading elevator manufacturers. IFE Elevator KONE Otis Elevator Company The Schindler Group ThyssenKrupp Elevator
Add to Compare
Access PE provides self contained access control for small and medium-sized companies. Its installation is extremely simple and fast. There is no need to install and administer a database system. The system is easy to use and enables a person with minimal training to create badges and administer access rights in a very short time. Specific event logging and reporting allows you to trace who was when and where on your company’s grounds.
Add to Compare
Retrieve historical events and alarms from the Command Centre database Monitor for live events and alarms as they are logged within the Command Centre database Acknowledge, process, and add notes to alarms Retrieve only the events that are relevant via filters. These filters are Event Group, Event Type, Event Source, Cardholder, Date and Time, and Division
Add to Compare
Distributed access control system with graphical alarm management Seamless integration and interaction with video, fire, intrusion and PA/VA systems via the common BIS platform High resilience thanks to a 4-tier system architecture and redundancy of critical components Integration of third-party products via open and secure protocols and SDK Efficient enrollment process that makes onboarding faster and more secure
Add to Compare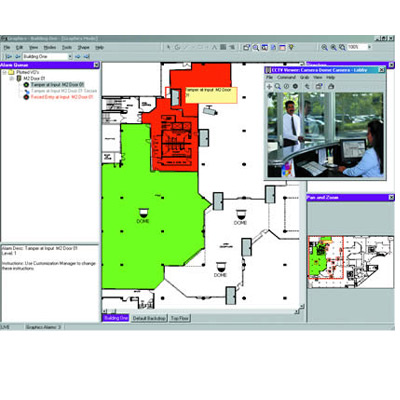
Velocity Security Management SystemHirsch's Velocity delivers total security in an all-in-one package: Access control: readers, keypads, biometrics, controllers for doors, gates, elevatorsAlarm monitoring, intrusion detection: sensors, alarm routing, automated responses, history/reports Video, CCTV: cameras, DVRs, links to analyticsIdentification management: smart cards, photo badges, integration with IDMS, CMS, watch listsInteroperability: with personnel system, network log-on, provisioning, command & control, central station, parking, HVAC, lighting, other devices, other databasesVelocity is network-ready & IT friendly. Velocity employs IT-centric tools such as integration with directory services, encrypted TCP/IP communications, and support of split server configurations and high-availability environments.The system is highly secure, requires little bandwidth, and is scalable to even the largest organisations. Velocity supports Unified Identity Management with a full line of smart card readers, biometrics and privacy-sensitive keypads. Velocity's open architecture, SDK, and built-in XML interoperability enable you to integrate Velocity with building automation and other systems. Velocity is designed to tightly integrate with personnel and network provisioning systems, allowing it to serve as the physical security component of an overall Role-Based Access Control (RBAC) and policy-based security management system. This approach can help enhance security, improve operational efficiency and reduce administrative and compliance costs.Velocity has earned numerous industry awards including an unprecedented five-time winning of the U.S. Security Industry Association's Product Achievement Award.
Add to Compare