Access Control Softwares (673)
Security management software package for access control. Integrates with existing card readers and alarm monitoring devices. It features a distributed processing architecture that utilises remote intelligent control. Features operation on windows, supports up to 30/4 doors; 1,000/500 individual badge numbers; 50 access levels/10 access levels; multi-language support; single workstation and migration path to AXxess 202/NS. Applications inlucde office buildings, small commercial and manufacturing facilities.
Add to Compare
Notifications is an optional licensed feature for Gallagher Command Centre that enables email or text messages to be sent to cardholders about events and alarms, as well as the imminent expiry of their cards or competencies. Notifications from Gallagher Command Centre are sent as email via a site’s mail server. To support notifications via SMS the site must subscribe to a ‘Bulk SMS Service Provider’. The Gallagher security system communicates with this provider via email specially formatted for final delivery via SMS. The provider then converts the email received from the Gallagher system to an SMS message and forwards it to the appropriate mobile network provider.
Add to Compare
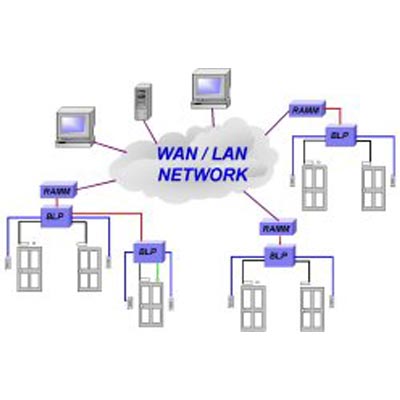
Symmetry Global is the ideal choice for organisations spread over a number of geographically dispersed sites. It allows each site to maintain autonomous operation and responsibility for its own security systems, while obtaining benefits from centralised administration, card management and alarm handling.
Add to Compare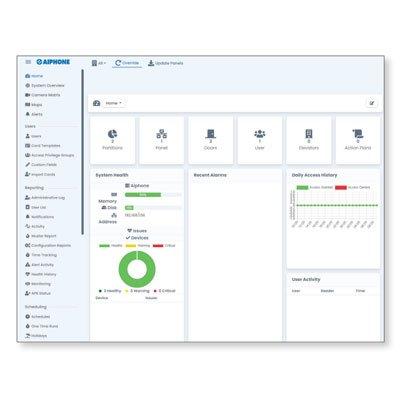
Small Business license of the AC Nio management software Manage a system of up to 80 doors and cameras, as well as elevators and unmanaged doors Allows up to five partitions and also supports Lightweight Directory Access Protocol (LDAP) integration
Add to Compare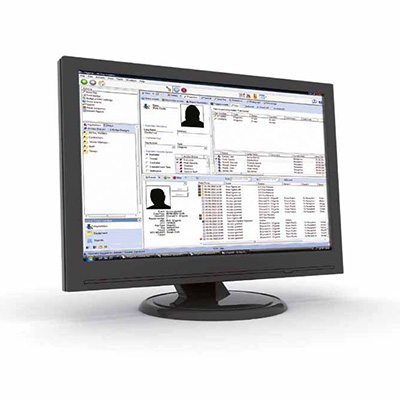
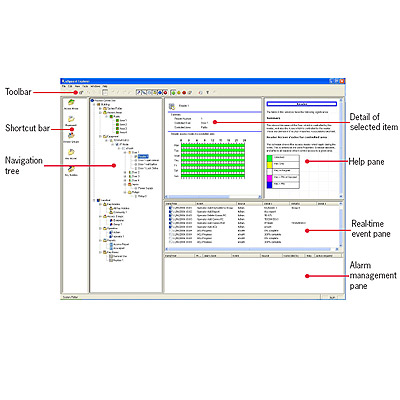
EXgarde is a fully featured Access Management PC software application that combines an extremely intuitive graphical user interface and powerful integration capabilities in a single package. Supporting multiple doors as standard with the option to extend this with an unlimited door licence, EXgarde meets the needs of even the largest of access control networks. With EXgarde PRO integration and expansion are key features and there are numerous possibilities to integrate with the latest CCTV and biometric technologies.
Add to Compare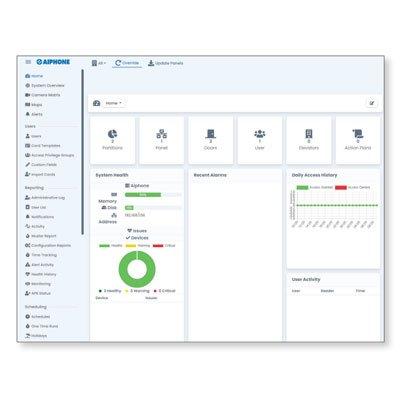
Management software for the AC Series access control system It is used to program a system and manage everyday functionality There are two license options - Essential license and Small Business license - available to accommodate different applications The Essential license can manage a system of up to 40 doors and cameras. It can be installed on a local server PC or on the AC-HOST embedded server The Small Business license can manage up to 80 doors and cameras, as well as elevators and unmanaged doors. This license allows up to five partitions and also supports Lightweight Directory Access Protocol (LDAP) integration
Add to Compare
ISONAS has taken its Software Development Kit to the next level and now offers a simple integration with the ISONAS Pure IP™ hardware solutions, giving customers real choice in their access control hardware. Access control evolution Partners can now create a powerful solution and add the next evolution in access control hardware to their product selection; while benefiting from future proofing their selections, reducing costs and giving them choice in their access control hardware. This comprehensive software development kit from ISONAS, makes it easy to integrate 3rd party access control software with the ISONAS Pure IP hardware families. ISONAS SDK platform While other SDK’s use low-level, error-prone TCP/IP communication to integrate, the ISONAS SDK platform supports high-level management mechanisms for event management, local discovery, communication and configuration. Using the .NET framework, the ISONAS SDK allows users to customise which features and functions of the ISONAS hardware to implement. With the ISONAS SDK, partners can add choice to their access control hardware solutions and go to market in no time. An open platform philosophy is nothing new to ISONAS. The company has a long history of integrations and with this significant investment into a modern SDK, ISONAS is furthering its mission to become a global player in open architecture hardware and software.
Add to Compare
User/Cardholder ManagementThe incredibly flexible user permissions provide an easy-to-use, building block method of assigning access and security rights to cardholders. Cardholder profiles are easily created by assigning multiple permissions with simple “Allow” and “Deny” functions. ReportingSingle-click reporting to review the areas cardholders have accessed, what areas cardholders have access to, search event and alarm history, programming history and much more. Easily export reports in a variety of common file formats. Schematic MapsRich graphics with interactive floor plans and maps. Effortlessly create maps using the built-in library of animated icons. Security and Alarm ManagementComplete alarm management with powerful automated actions. Operator PermissionsManage the operators that use Integriti software. Easily customise and define their access permissions levels with fine control. Audit TrialThe amazingly powerful forensic audit trail records every programming change made by all operators and provides the ability to “roll-back” to any change in the past. Data ImportationImport cardholder data in a variety of file formats from third party systems. System Health MonitoringMonitor the health of both the Integriti hardware and software. Proactive notifications can alert security operators and security contractors if maintenance is required. SkyTunnel ConnectivitySkyTunnel is an industry-first cloud based service that provides hassle free connectivity of Integriti hardware, software and mobile apps. Intuitive DesignThe Integriti System Management Suite is a true cutting-edge solution. Integriti boats a contemporary and intuitive design that is simple to use and easy to learn. System Designer and GateKeeper ApplicationsSystem Designer is used for all aspects of system programming and configuration. GateKeeper is a dedicated application to simplify day to day monitoring and control of the Integriti system. Modern Client/Server ArchitectureIntegriti employs a client/server architecture and is fully compatible with the latest computing platforms and Microsoft SQL databases.
Add to Compare
C•CURE IQ Microservices is designed to allow smaller components of software (ex: software drivers) to interact with each other over a standard network protocol such as HTTP. With C•CURE IQ Microservices, the business logic is split into individually deployable services that are isolated from other services by network-based interfaces. This re-design allows for increased system scale, resiliency, and improved cybersecurity, by isolating the individual processes into their own containers. C•CURE IQ Microservices are built for the Kubernetes® platform. Kubernetes (also known as K8s®) is an open-source system for automating deployment, scaling, and management of containerized applications.
Add to Compare
C•CURE IQ Microservices is designed to allow smaller components of software (ex: software drivers) to interact with each other over a standard network protocol such as HTTP. With C•CURE IQ Microservices, the business logic is split into individually deployable services that are isolated from other services by network-based interfaces. This re-design allows for increased system scale, resiliency, and improved cybersecurity, by isolating the individual processes into their own containers. C•CURE IQ Microservices are built for the Kubernetes® platform. Kubernetes (also known as K8s®) is an open-source system for automating deployment, scaling, and management of containerized applications.
Add to Compare
C•CURE IQ Microservices is designed to allow smaller components of software (ex: software drivers) to interact with each other over a standard network protocol such as HTTP. With C•CURE IQ Microservices, the business logic is split into individually deployable services that are isolated from other services by network-based interfaces. This re-design allows for increased system scale, resiliency, and improved cybersecurity, by isolating the individual processes into their own containers. C•CURE IQ Microservices are built for the Kubernetes® platform. Kubernetes (also known as K8s®) is an open-source system for automating deployment, scaling, and management of containerized applications.
Add to Compare
Retrieve and report on stored information including events, alarms, cardholders, cardholder location, resource utilization, and site items. Configure reports to run on a repeating schedule or in response to events such as a fire alarm. Schedule the generation of reports and email automatically to recipients. Access reports easily through a ‘find reports’ viewer or ‘favorites’ list within Command Centre. Filter report content using parameters such as competency status, card type and cardholder’s last entered zone. Configure the report page layout and file output type (.doc, .xls, .pdf or .csv). Report on visitor data (when used with optional visitor management tools). View additional reports, including evacuation, access, time and contextual reporting. Report on security events from an individual server, or from multiple servers within a multi-server network.
Add to Compare
Access control has become a vital component of any security concept worldwide. The protection of intellectual property rights, prevention of theft and sabotage or simply compliance requirements - there are a multitude of reasons why companies of all kinds need to use a comprehensive access control system to restrict, manage and control access to their facilities. However, operated in isolation from other safety and security systems, even the most sophisticated access control system cannot really live up to its promises. In such an environment, operation and monitoring can quickly turn into a nightmare, as each system has its own architecture, its own user interface and its own management tool. This is why more and more organizations are looking out for an access control solution that easily integrates with video monitoring, intrusion detection and sometimes even visitor management to form a homogeneous security system with a consistent user interface and central management and operations.Moreover, suppliers are more and more often faced with requirements of their customers to supply a documentation of all access attempts, whether successful or not, to protect against industrial espionage. To fulfill this requirement, not only employee access must be captured and recorded, but also the entire visitor traffic. Video integration for more safetyWhile modern access control systems allow an efficient management of access rights, they are rather powerless against abuse if operated on their own. In critical environments it is mandatory to add a second layer of security by integrating access control with some kind of video surveillance. To prevent abuse, all access requests can then trigger one or more video cameras. Integrated systems can provide alarm verification, instantly displaying live video images from nearby cameras when there is an alarm event at a door - such as when a person presents an unauthorised credential or when a door is forced open. Forensics can also benefit from such integration if the video recordings are referenced in the access control system's event log. Such a feature greatly facilitates identification, retrieval and playback of past events and alarms if necessary.Open standards ease integrationIntegrating access control, video monitoring, and intrusion detection can be rather easy when all components come from the same vendor and if this vendor also offers a management platform like the Building Integration System from Bosch for all of them. Integrated systems "off the shelf" can greatly ease installation and configuration of the security solution. Logical integration eliminates the need for multiple software platform and interfaces -- resulting in fewer complications and greater event-driven functionality as well as reduced installation time and costs. What's more, this kind of integration also promises more efficient operation and a clearly reduced need for training, but above all also a higher security level. An open standards-based management system even makes sense in those cases where one vendor supplies everything, as it opens up the entire installation for future expansion.User interface is keyAn integrated security system is a very complex apparatus, and if this complexity is not hidden from the user, the system will be highly prone to human error and maloperation. Such systems do need very clear and intuitive user interfaces, avoiding information overload while offering all the information that is currently needed. This is even more important when several components or dialogs are open, which will often be the case if you deal with access control, video surveillance and maybe intrusion detection from the same console.
Add to Compare
CrossChex Mobile is the mobile version of CrossChex Software, which lets you add and manage everyone and grant access rights to them on a smartphone. Your staff can easily clock in and access to any places with just one click on the phone. Any of Anviz access control devices with Bluetooth function can be added to CrossChex Mobile, and the time attendance device with Bluetooth function can be also added to CrossChex mobile to have a clock in function and realize the access control function with linked to a Bluetooth micro access controller. CrossChex Mobile is suitable for the application in small offices, retail stores, gyms, clinics, etc.
Add to Compare
A mobile app for the AC Series access control system that allows users to unlock doors from a smartphone or tablet Administered by AC Nio, track user and visitor activity Assign users to the entire site or specific partitions Works on the local network or off-site with port forwarding Create favorite lists of frequently used doors Issue temporary Visitor Passes by text or email Available for Apple® iOS and Google Android™ smartphones or tablets
Add to Compare
Access control specialist TDSi has launched its new MIFARE Programmer, which offers users the ability to specify their own sectors and keys on their MIFARE access cards. Together with the ability to re-configure TDSi's standard sector readers to any desired code (without the need for any other parties to be involved), the MIFARE Programmer ensures confidentiality of security data and access control.To make sure it doesn't inadvertently become a weak point of security itself, TDSi's MIFARE Programmer uses a highly secure user login to protect the ability to programme user cards from unauthorised users. Having control of MIFARE security details also offers a number of other key benefits: Use pre-assigned sequential numbers - The MIFARE Programmer provides an effective method of card programming which eliminates potential duplication problems, Read and identify existing cards - users can identify existing cards and sector usage before migrating existing system cards, Log all cards issued - The MIFARE Programmer provides a history of cards which have been issued (for future reference), Multiple card number options - The user can utilise a unique number, custom number or CSN to program a sector, providing increased flexibility, Dual decode options - The MIFARE Programmer allows users to decode the new 7 byte UID using TDSi's format or NXP's format, for increased flexibility, Check which sectors are used - This built-in function allows users to check which sectors have already been used. This is ideal if you want to migrate existing MIFARE CSN cards that may be utilised for other aspects (such as cashless vending) to a more secure sector operation. TDSi's John Davies comments on the MIFARE Programmer, "For companies that need the highest levels of protection; the ability to protect your security codes across the board is a very attractive proposition. Being able to programme your own MIFARE cards and readers means you can close a potential gap in security that comes from pre-programmed systems. We believe this is a unique solution that offers real peace of mind. It has been developed from feedback we have had from installers and users, who advised that it would be highly desirable choice for both security and convenience."
Add to Compare
CEM AC2000 Data Import Tool allows system administrators to import 3rd party cardholder details into the AC2000 Personnel application, which stores cardholder information on the access control system. It simplifies the bulk loading of data from a 3rd party system which is typically required during a new system installation. This removes the need for duplicate data entry and offers users a quick and efficient method of importing data into the AC2000 system. Using the interface tool, an unlimited number of records, including cardholder photographs, can be easily brought into the AC2000 system, eradicating the requirement for customised software development or time consuming database scripts.
Add to Compare
TDSi 4420-2401 is an optional visitor management module to the EXgarde platform with simplified front-end users which makes managing visitors much easier. Visits can be scheduled in advance or on the day with this intuitive module. Providing a cost effective and dependable visitor management function, EXvisitor enables an organisation to manage and track visitors and their hosts across a site.
Add to Compare
Access PE provides self contained access control for small and medium-sized companies. Its installation is extremely simple and fast. There is no need to install and administer a database system. The system is easy to use and enables a person with minimal training to create badges and administer access rights in a very short time. Specific event logging and reporting allows you to trace who was when and where on your company’s grounds.
Add to Compare
The latest release of the AC2000 suite of access control and security management software. AC2000, AC2000 Airport and AC2000 Lite version 7.0 are now available with a range of new features that increase the performance, simplicity and scope of the system along with a number of additions that improve functionality. Card Validation from online readers AC2000 Users can now validate cards using any online reader, either Ethernet or Serial, without the need to have a dedicated validation reader. AC2000 Intercom CEM AC2000 Intercom software can now be deployed as a standalone installation on dedicated intercom workstations where full AC2000 system functionality is not required. AC2000 now also supports the functionality to record emerald intercom (only available in emerald TS200/TS300 terminals) voice communication to audio files and store on the AC2000 central server. Integrations AC2000 now supports full two way integration with Salto off-line locks utilising SHIP (Salto Host Interface Protocol). This bi-directional interface links directly to the Salto database server. With the release of v7, AC2000 now supports a fully featured interface with Genetec Security Center, a unified platform with IP surveillance. This new link allows alarms and video footage from Genetec Security Center to be fully integrated with AC2000. Enhanced emerald functionality In AC2000 v7 a new pre-door mode allows for the display of a configurable personal message to the cardholder on the emerald terminal. This release also enables system administrators to use AC2000 WEB to upload their company logo to display on the emerald home screen.
Add to Compare
The ACURT2 is an integrate access control, video surveillance, alarm monitoring, and photo ID badging with the Topaz Access Control System. Topaz is packaged with everything you need to get your security system up and running quickly and reliably.
Add to Compare
TDSi EXgarde’s integration with Aperio offers a new level of remote lock functionality with a global leader in door opening solutions. Using Aperio alongside TDSi’s core systems allows greater flexibility in remote areas where access control may be more difficult to implement.
Add to Compare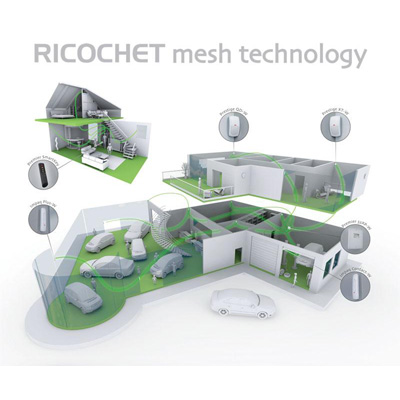
Ricochet Monitor software, when installed on a laptop and connected to a RICOCHET enabled wireless expander, provides greater visibility and control over the wireless system performance than ever before. From a simple, intuitive menu screen all device status is available at a glance, with clear graphics highlighting signalling performance. Device attributes can be configured and distributed across the network in seconds thanks to an innovative ‘global poll' function that communicates to all devices within moments.
Add to Compare
CEM SWENET256 is an Ethernet reader controller software for 256 doors. It is a software controller required for use with Ethernet based CEM readers and devices as part of the AC2000 SE (Standard Edition) and AC2000 AE (Airport Edition) access control systems. The RTC is used with CEM Ethernet devices such as the emerald touch screen reader, S610e reader, S610f reader, Etherprox reader, S3030 portable reader range, eDCM 300 (Door Control Module), eDCM 300 Input/Output Module and the EIOC (Ethernet Input/Output Controller). The RTC Ethernet software offers an added layer of system resilience as it is capable of operating independently from the central CDC server should communications between the two be temporarily lost.
Add to Compare
Easy registration and transmission of fingerprint data using wizard interface. Can be seen fingerprint's image and quality of fingerprint using USB fingerprint scanner(Hamster). Fingerprint quality check. Supports serial and TCP/IP communication (Required external converter). Supports step by step workflow for fingerprint data upload and download. ID registration process convenient and easy to enter data. Supports Text, Excel data export. Supports server and client system. Support MS-SQL server database.
Add to Compare
CEM SYS/101/300 is a PC with SWENET256 software installed. The SWENET256 is required for use with Ethernet based CEM readers and devices as part of the AC2000 SE (Standard Edition) and AC2000 AE (Airport Edition) access control systems. The RTC is used with CEM Ethernet devices such as the emerald touch screen reader, S610e reader, S610f reader, Etherprox reader, S3030 portable reader range, eDCM 300 (Door Control Module), eDCM 300 Input/Output Module and the EIOC (Ethernet Input/Output Controller). The RTC Ethernet software offers an added layer of system resilience as it is capable of operating independently from the central CDC server should communications between the two be temporarily lost.
Add to Compare
CEM SWXML AC2000 XML interface provides a simple and efficient way to import basic cardholder details into the AC2000 access control system. The import process allows incremental updates from a third party source and will support a large single batch import that is typically required during a new system setup. It also provides customers with a frequent data transfer link from many third party systems such as Human Resource systems. The interface enables the bulk adding and updating of personnel records, such as surname and card number.
Add to Compare