Access Control Cards, Tags & Fobs (568)

Can be attached to a watch or bracelet for convenient access through doors on a Net2 system To issue a Watchprox token the user’s details are entered using the PC software. The token number is then entered by presenting the Watchprox to the desktop reader Once programmed into the software the token is ready for use Uses Hitag2 technology with proprietary encoding which includes an authentication protocol in the form of a password exchange between the token and the reader
Add to Compare
Utilises highly secure 13.56MHz MiFare DESFire smart card technology Fully ISO / IEC 14443 A 1-4 compliant Pre-personalised card memory allowing for usage in other systems such as cashless vending Advanced Encryption Standard (AES) -128-bit or Triple DES (3DES) encryption between the card and the reader Meets ISO standards for thickness for use with all direct image and thermal transfer printers Add a magnetic stripe, barcode, anticounterfeiting, or photo ID to the card Compatible with the CEM sPass reader, S700 reader range, and the emerald touch screen reader range
Add to Compare
Utilises highly secure 13.56MHz MiFare DESFire smart card technology Fully ISO / IEC 14443 A 1-4 compliant Pre-personalised card memory allowing for usage in other systems such as cashless vending Advanced Encryption Standard (AES) -128-bit or Triple DES (3DES) encryption between the card and the reader Meets ISO standards for thickness for use with all direct image and thermal transfer printers Add a magnetic stripe, barcode, anticounterfeiting, or photo ID to the card Compatible with the CEM sPass reader, S700 reader range, and the emerald touch screen reader range
Add to Compare
Downloadable interface module providing a complete interface between 4 readers and a control panel. Has ability to receive a download of the database from the controller, 12 supervised inputs and digital strike control. Supports a variety of card readers including the Apollo AP-400, 410, 501, 502 and 400/410 reader and keypad combo.
Add to Compare
The Stanley proximity tokens are available in seven distinctive colours and are fully interchangeable with the existing PAC® token range and are also compatible with Stanley's PAC, Easikey, Oneprox and GDX Indigo proximity readers. Stanley tokens can be programmed into Stanley’s PAC and GDX residential and commercial access control systems so that the user's movement can be monitored and the building protected. Each Stanley token has a unique ID code and need only be held near a door reader for the code to be read and access granted or denied in less than a second. It is compatible with the following readers; PAC Easikey™, PAC® and PAC Oneprox™ GDX Indigo™.
Add to Compare
The Stanley proximity tokens are available in seven distinctive colours and are fully interchangeable with the existing PAC® token range and are also compatible with Stanley's PAC, Easikey, Oneprox and GDX Indigo proximity readers. Stanley tokens can be programmed into Stanley’s PAC and GDX residential and commercial access control systems so that the user's movement can be monitored and the building protected. Each Stanley token has a unique ID code and need only be held near a door reader for the code to be read and access granted or denied in less than a second. It is compatible with the following readers; PAC Easikey™, PAC® and PAC Oneprox™ GDX Indigo™.
Add to Compare
The Stanley proximity tokens are available in seven distinctive colours and are fully interchangeable with the existing PAC® token range and are also compatible with Stanley's PAC, Easikey, Oneprox and GDX Indigo proximity readers. Stanley tokens can be programmed into Stanley’s PAC and GDX residential and commercial access control systems so that the user's movement can be monitored and the building protected. Each Stanley token has a unique ID code and need only be held near a door reader for the code to be read and access granted or denied in less than a second. It is compatible with the following readers; PAC Easikey™, PAC® and PAC Oneprox™ GDX Indigo™.
Add to Compare
The Stanley proximity tokens are available in seven distinctive colours and are fully interchangeable with the existing PAC® token range and are also compatible with Stanley's PAC, Easikey, Oneprox and GDX Indigo proximity readers. Stanley tokens can be programmed into Stanley’s PAC and GDX residential and commercial access control systems so that the user's movement can be monitored and the building protected. Each Stanley token has a unique ID code and need only be held near a door reader for the code to be read and access granted or denied in less than a second. It is compatible with the following readers; PAC Easikey™, PAC® and PAC Oneprox™ GDX Indigo™.
Add to Compare
The new key card offers a maximum range of up to 50m. The new triple-function Net2Air keycard operates as a normal hands free token on doors equipped with a hands free interface and, by operating the keycard buttons, as a long range access card.
Add to Compare
The proximity read-only clam shell card offers universal compability with the Wiegand IF reader type W 3 The card includes an embedded antenna, and an RFID integrated circuit including a printed number on the face of the card enabling contactless reading by readers Reliable and interference free Strong, flexible and resistant to breaking Photo ID compatible Pocket size The card is durable with IP 68 and can be fully submerged, all the electronics are sealed inside
Add to Compare
The proximity read-only tag offers universal compability with the Wiegand IF reader type W 3 The tag includes an embedded antenna, and an RFID integrated circuit enabling infinite numbers of reads by Wiegand type W3 readers The key-ring sized credential tag is durable with IP 68 and can be fully submerged, all the electronics is sealed inside
Add to Compare
ID card for contactless Esser readers without label (026368). ID card for contactless readers with primary colour white with Esser logo (026370). ID card with magnetic strip for contactless readers, with Esser label (026371). ID card with unencoded magnetic strip for contactless Esser readers, white (026372).
Add to Compare
The proximity read-only card offers universal compability with the Wiegand IF reader type W 3 The card includes an embedded antenna, and an RFID integrated circuit including a printed number on the surface of the card enabling contactless reading by readers The credit card sized card conforms to the ISO-standard size enabling surface printing with conventional ISO compatible card printers The card is durable with IP 68 and can be fully submerged, all the electronics are sealed inside
Add to Compare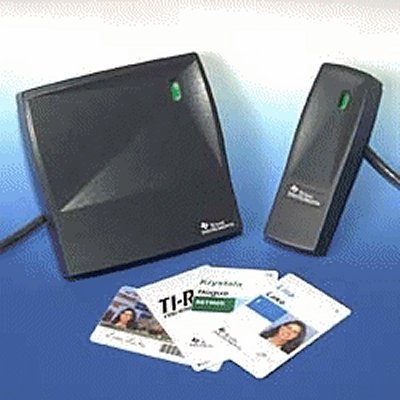
Texas Instruments' latest contactless ID badge, card and reader technology provides high specification access control solutions at economical and competitive prices. Key technological features and benefits include: Latest 13.56 MHz RFID technology meeting ISO 15693 Standards for contactless cards - means inter-operation with other ISO products ISO 7810 physical format for easy, low-cost card printing and customisation 2K-bits of user memory for storing secure access control data, biometric authentication etc High speed data transfer for faster reading - especially at peak periods Smart anti-collision protocol allows the system to operate normally even if more than one card is in the read area Choice of readers including a small mullion unit and wall-plate models, both available in black or grey colours Cards can be re-programmed or updated 'at the door' for easier management Higher security applications, the readers can encrypt and decrypt security data including biometrics from the cards
Add to Compare
Bosch RF3334 is a four-button wireless key fob that transmits at a frequency of 304.00 MHz. It allows to arm and disarm the security system or send a panic alarm. Programmed with a unique code, the fob works exclusively with compatible security system. The two option buttons are user-defined to perform additional functions.
Add to Compare
The Tag will transmit a Radio Frequency (RF) signal at a pre-set time-interval. The Tag life is estimated at 5 years at a transmission time interval of approximately 1.5 seconds. Battery status can be inferred by interrogating the internal Tag Age Counter Value. The transmitted Tag data includes Customer Site Code (CSC), Tag ID, Tag Age Counter Value, Movement Alarm and Tamper Alarm status. For protection against adverse environmental conditions, Link-it™ Tags are encapsulated in a moulded plastic case, which is ultrasonically sealed during the manufacturing process. The Slimline Tag is generally used for personnel tagging, although it may be used in other applications such as asset monitoring.
Add to Compare
The CK-IR7 is powered by a replaceable battery and is compatible with all CyberLock cylinders. The off-the-shelf 3-volt lithium batteries can easily be changed in the field. Programmed with access permissions for each key holder, CyberKey smart keys serve as the gate keeper for the CyberLock system. In addition, they provide the power needed to energise the CyberLocks.
Add to Compare
An internal lithium battery powers Link-it™ series of Active Tags. The Domino Tag will transmit a Radio Frequency (RF) signal at a pre-set timeinterval. The Tag life is estimated at 5 years at a transmission time interval of approximately 1.5 seconds. The transmitted Tag data includes Customer Site Code (CSC), Tag ID, Tag Age Counter Value, Movement Alarm and Tamper Alarm status. For protection against adverse environmental conditions, Link-it™ Tags are encapsulated in a moulded plastic case, which is ultrasonically sealed during the manufacturing process. The Domino Tag is generally used for asset tagging. The mounting and affixing of a Tag depends on the type of application.
Add to Compare
An internal lithium battery powers the Wavetrend W-series of Active Tags. The Domino Tag will transmit a Radio Frequency (RF) signal at a pre-set time-interval. The Tag life is estimated at 5 years at a transmission time interval of approximately 1.5 seconds. Battery status can be inferred by interrogating the internal Tag Age Counter Value. The transmitted Tag data could include Customer Site Code (CSC), Tag ID, Tag Age Counter Value, Movement Alarm and Tamper Alarm status. For protection against adverse environmental conditions, Wavetrend Tags are encapsulated in a moulded plastic case, which is ultrasonically sealed during the manufacturing process. The Domino Tag is generally used for asset tagging. The mounting and affixing of a Tag depends on the type of application. The standard method is by VHB type double-sided adhesive tape.
Add to Compare
The Secure Card will transmit a Radio Frequency (RF) signal at a pre-set time-interval. The Tag life is estimated at 5 years at a transmission time interval of approximately 1.5 seconds. Battery status can be inferred by interrogating the internal Tag Age Counter Value. The transmitted Tag data could include optional Customer Site Code (CSC), Tag ID, Tag Age Counter Value, movement Alarm and Tamper Alarm status, Tamper logged status, etc. For protection against adverse environmental conditions, Wavetrend Tags are encapsulated in a moulded ABS plastic case. The Tag can be configured to accommodate Wiegand interfacing. The Tag is generally used for personnel tagging, although it may be used in other applications such as asset monitoring.
Add to Compare
Water and dust resistant Arm, disarm and panic functions Assigned by user for accurate reporting of open close signals LED indicator Programmable option buttons The wireless keyfob with synchronised encryption features increased immunity to replay attacks, providing even more reliable system security
Add to Compare
The Wiegand interface unit converts data from the Wavetrend Buffer L-CB100 or the Wavetrend Reader L-RX201 to standard Wiegand (bit selectable) protocol as commonly used in the Access Control Industry. The unit comprises of a plug-in module, consisting of a 8-way screw terminal for the input wires from the Receiver Network and an 8-way terminal for the seven wires to a Wiegand access controller. The user should order Wiegand encoded Tags for use with this unit.
Add to Compare
The Bracelet Tag will transmit a Radio Frequency (RF) signal at a preset time-interval. The Tag life is estimated at 5 years at a transmission time interval of approximately 1.5 seconds. Battery status can be inferred by interrogating the internal Tag Age Counter Value. The transmitted Tag data includes Customer Site Code (CSC), Tag ID, Tag Age Counter Value, Movement Alarm and Tamper Alarm status. For protection against adverse environmental conditions, Link-it™ Tags are encapsulated in a moulded plastic case. The L-TG1200 is generally used for hospital patient tagging, although it may be used in other applications such as personnel monitoring. The Tag can be configured to accommodate Wiegand interfacing.
Add to Compare
Water and dust resistant Arm, disarm and panic functions Assigned by user for accurate reporting of open close signals LED indicator The wireless keyfob with synchronised encryption features increased immunity to replay attacks, providing even more reliable system security
Add to Compare
The CK-RXD2 is powered by a rechargeable battery and is compatible with all CyberLock cylinders. The key can be recharged via the USB port from a computer, car charger, or any other compatible USB device. Additionally, a variety of stand-alone recharging stations and communication devices with recharging capabilities are available. Programmed with access permissions for each key holder, CyberKey smart keys serve as the gate keeper for the CyberLock system. In addition, they provide the power needed to energise the CyberLocks.
Add to Compare
Used to operate CyberLock cylinders and FlashLock access points The Bluetooth 5.0 is activated with the push of a button and allows users to update access permissions on the go using an Androidor iOS app It has a convenient micro-USB port for charging on the go Cache access permissions and delay activation until the user arrives on site Fully customisable permission schedules Remotely update access permissions
Add to Compare
Memory contains encrypted access codes & records up to 12,000 audit trail events Compatible with Cyber Audit-Web Basic or Enterprise (v.9.0 or later) Charge via the key tip or using the micro USB port Individually manage fully customisable permission schedules
Add to Compare
The Link-it™ KeyFOB Active Tags are powered by an internal battery. The Tag will, for the duration of its life, transmit a Radio Frequency (RF) signal at a pre-set time-interval. The Tag life is estimated at 5 years at a transmission time interval of approximately 1.5 seconds. Additionally, the KeyFOB has a panic button, and such transactions will either be logged when out of reader range, or be reported immediately when within reader range. The transmitted Tag data includes Customer Site Code (CSC), Tag ID, Tag Age Counter Value, Panic Alarm status. For protection against adverse environmental conditions, the Link-it™ KeyFOB Tag is encapsulated in a moulded plastic case. The KeyFOB Tag is generally used for key tagging, although it may be used in other applications such as personnel monitoring. The Tag can be configured to accommodate Wiegand interfacing.
Add to Compare
Used to operate CyberLock cylinders Expanded memory records 12,000 key events or 250 lock downloads Extends battery life and allows users to update access permissions on the go using an Android or iOS app and smartphone Powerful new features with software enhancement module, like delayed activation for locations without cellular service and Variable Temporary Access (2 minutes – 72 hours) provide ultimate control Pairs with mmart devices running the CyberAudit® Link App Individually manage fully customisable permission schedules Reports audit trails within seconds for accurate record keeping
Add to Compare
Used to operate CyberLock cylinders It has memory that contains encrypted access codes, a list of locks it may access, schedules of authorised dates and times it may access locks, and a begin-end date range during which the key will operate The battery from a CyberKey energises the electronics within a CyberLock cylinder Rechargeable battery
Add to Compare
Works in conjunction with CyberLock, FlashLock, and RFID access points Features dual-mode Bluetooth technology for in-the-field updates LCD screen provides a menu for viewing expirations and battery status as well as selecting key functions Android and iOS compatible communicators Memory contains encrypted access codes & records up to 12,000 audit trail events
Add to Compare
Has an increased memory capacity with the infrared technology and replaceable battery The memory can hold up to 12,000 locks or audit events, or up to 100 lock downloads Replaceable 3 Volt Lithium CR2 battery IR communications for use with the IR Encoder 10 Individually manage fully customisable permission schedules and record audit trails
Add to Compare








